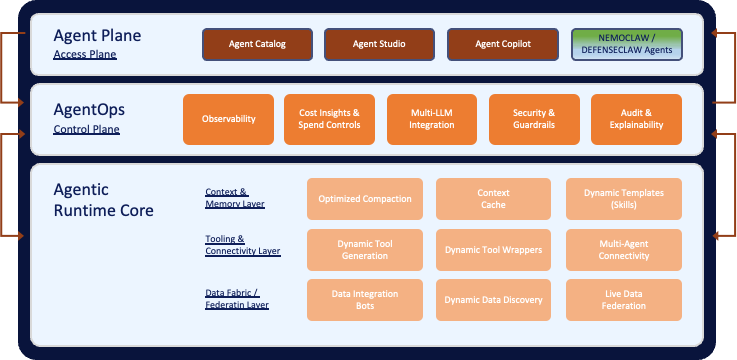
The agentic AI security stack is taking shape , fast. At GTC 2026, NVIDIA unveiled NemoClaw, an open-source stack that wraps OpenClaw with enterprise-grade privacy controls, local inference via Nemotron models, and the OpenShell sandboxed runtime. Days later at RSAC 2026, Cisco launched DefenseClaw, an open-source governance framework that scans every agent skill, MCP server, and plugin before admission , and enforces block/allow policies at runtime with sub-two-second enforcement.
Together, NemoClaw and DefenseClaw answer a critical question: Can I trust this agent to run safely?
But there’s a question they don’t answer , and it’s the one that determines whether your agentic investment actually delivers operational outcomes: Can this agent find, federate, and reason over the right data across my fragmented enterprise?
That’s where Fabrix.ai comes in.
The Stack as It Stands Today
Let’s map what NemoClaw and DefenseClaw actually do , because the clarity matters.
- NVIDIA NemoClaw provides a secure agent runtime. OpenShell enforces infrastructure-level sandboxing: kernel isolation, deny-by-default network access, YAML-based policy enforcement, and a privacy router that keeps sensitive data local while routing complex reasoning tasks to frontier cloud models. It’s the secure chassis , the equivalent of a hardened OS for autonomous agents.
- Cisco DefenseClaw adds the governance layer. Its scan engine runs five tools , skill-scanner, mcp-scanner, a2a-scanner, CodeGuard static analysis, and an AI bill-of-materials generator , against every component before it’s allowed into the agent environment. At runtime, a content scanner inspects every message flowing in and out of the agent’s execution loop. When DefenseClaw blocks something, it’s not advisory , sandbox permissions are revoked, files are quarantined, and MCP server endpoints are removed from the network allow-list.
And critically, DefenseClaw streams all of this telemetry , scan findings, block/allow decisions, prompt-response pairs, tool calls, policy enforcement actions, and alerts , into Splunk as structured events from the moment an agent comes online. Every agent is, in Cisco’s language, “born observable.”
- Splunk’s Agentic SOC then acts on that telemetry. At RSAC 2026, Cisco announced six specialized AI agents for the SOC , a Detection Builder Agent, SOP Agent, Triage Agent, Malware Threat Reversing Agent, Guided Response Agent, and Automation Builder Agent , alongside Exposure Analytics for continuous asset discovery, Detection Studio for unified detection engineering, and Federated Search for cross-environment correlation.
This is a formidable security stack. But it has a fundamental gap.
The Missing Layer: Enterprise Operational Context
The agent runtime platform solves the mechanics of agent execution , how agents reason, plan, use tools, manage memory, and spawn sub-agents. What it doesn’t address is what agents reason about when they’re operating in an enterprise environment.
Consider what happens when you deploy a NemoClaw-sandboxed, DefenseClaw-governed agent into an enterprise ITOps, NOCOps, or SecOps environment. The agent is secure. It’s observable. It’s governed. And it’s immediately confronted with a reality that the runtime wasn’t designed for:
- Data fragmentation: Operational data is scattered across 15–30 tools , observability platforms, ITSM systems, CMDBs, log aggregators, APM tools, network monitoring, cloud consoles, security platforms
- No semantic layer: Raw API responses from MCP servers and tools are just payloads. They lack entity relationships, service topology, business context, and causal linkages
- No cross-domain correlation: An alert in one system, a change in another, a capacity threshold in a third , the agent has powerful reasoning capabilities but no unified operational knowledge graph to reason over
- No ontological grounding: The agent can query Splunk, but it doesn’t understand that “this alert on server X relates to change request Y deployed by team Z, impacting revenue-critical service W, with a blast radius extending to 14 downstream microservices”
This isn’t a security problem. It isn’t a runtime problem. It’s a data intelligence problem , and it’s the reason 85% of enterprises experimenting with AI agents have only 5% in production (per Cisco’s own RSAC 2026 survey).
The agent runtime needs an enterprise brain. That brain is Fabrix.ai.
How Fabrix.ai Completes the Agent Stack
Fabrix.ai operates in a hybrid architecture alongside the NemoClaw/DefenseClaw stack , functioning both
- as a context and data service that the agent runtime consumes, and
- as a unified agentic control plane running its own purpose-built operational agents that share a common intelligence layer with the broader agent ecosystem.
The Architecture: Two Agent Populations, One Operational Brain
- Layer 1 , Fabrix.ai as Context Service for Agent Runtimes
NemoClaw-hosted agents connect to Fabrix.ai’s Agentic Data Federation layer through MCP servers and APIs. When an agent needs operational context , service dependencies, entity relationships, historical patterns, cross-domain correlations , it queries Fabrix.ai the same way it queries any tool. But instead of getting raw API payloads, it gets ontology-enriched, entity-aware context that dramatically improves reasoning quality.This is non-invasive integration. The agent runtime doesn’t change. DefenseClaw still scans and governs. OpenShell still sandboxes. Fabrix.ai simply becomes the most powerful “tool” in the agent’s toolkit , the one that provides operational intelligence rather than raw data.
- Layer 2 , Fabrix.ai’s Unified Agentic Control Path with its Purpose-Built Operational Agents
Alongside the NemoClaw/DefenseClaw agent runtime, Fabrix.ai operates its own purpose-built agents for enterprise ITOps, NOCOps, and SecOps. These aren’t general-purpose personal AI assistants , they’re domain-specific operational agents with deep knowledge of infrastructure patterns, incident workflows, change management, and service topology.” - Unified Agentic Control Plane – The Shared Intelligence Layer , ECL Ontology and Agentic Data Federation
Both agent populations , the NemoClaw-hosted agents and Fabrix.ai’s operational agents , draw from the same underlying intelligence: Fabrix.ai’s ECL (Entity-Context-Linking) Ontology and Agentic Data Federation layer. This shared “system of truth” ensures consistent operational context regardless of which agent is reasoning over it.
What Fabrix.ai Concretely Delivers
- Agentic Data Federation: Connecting Agents to Enterprise Reality
Neither NemoClaw nor DefenseClaw provides the data fabric that feeds agents with operational context. Fabrix.ai’s Agentic Data Federation layer connects siloed data sources , observability platforms, ITSM systems, CMDBs, log aggregators, APM tools, network monitoring , and presents them as a unified, queryable context layer.This isn’t traditional ETL that moves data into a warehouse. It’s a federated architecture where agents query data in place, enriched with entity relationships and business context through the ECL Ontology. The shift from ETL (Extract-Transform-Load) to ECL (Entity-Context-Linking) is foundational: meaning and relationships become first-class citizens, not afterthoughts bolted onto data pipelines.
- ECL Ontology: From Raw Payloads to Semantic Understanding
The OpenClaw/NemoClaw ecosystem assumes agents will call MCP servers and tools to get data. But raw tool outputs lack the semantic structure agents need for genuine operational reasoning.Fabrix.ai’s ECL layer builds an ontology-driven knowledge graph that gives agents entity-aware, relationship-rich context. This is the difference between an agent that can “query Splunk” and an agent that understands the causal chain from an alert to a root cause to a blast radius to a business impact , across data from dozens of sources that were never designed to interoperate.
- Operational Observability: The Other Half of “Born Observable”
DefenseClaw makes agents “born observable” from a security perspective , every scan, block decision, tool call, and prompt-response pair gets telemetered to Splunk. Cisco’s Agentic SOC then acts on that telemetry with six specialized AI agents for detection, triage, and response , Detection Builder, SOP Agent, Triage Agent, Malware Threat Reversing Agent, Guided Response Agent, and Automation Builder Agent.But there’s a parallel observability requirement: operational observability , the unified view of infrastructure health, service dependencies, incident patterns, and business impact that agents need to reason about operational problems. Fabrix.ai’s Agent Runtime Core provides this through:
-
- Universal Tooling & Connectivity Engine: Connectors to 150+ data sources across observability, ITSM, security, and infrastructure platforms
- Ontology Layer: Entity-relationship mapping that turns raw data into contextual knowledge
- Context Engine: The reasoning substrate that lets agents correlate across domains and time
This operational observability layer sits alongside the security observability that DefenseClaw provides through Splunk. Together, they give agents both governance and intelligence.
From MTTR to MTTP: The Outcome That Security Alone Can’t Deliver
The entire NemoClaw → DefenseClaw → Splunk Agentic SOC pipeline is oriented around accelerating response: faster scanning, faster triage, faster detection, faster remediation are all designed to reduce Mean Time to Respond (MTTR).
Fabrix.ai’s value proposition operates on a different axis entirely: the shift from MTTR to MTTP , Mean Time to Prevention.
By feeding ontology-enriched, cross-domain context into agents (both NemoClaw-hosted and Fabrix.ai-native), Fabrix.ai enables agents that don’t just respond to incidents but anticipate and prevent them by recognizing precursor patterns across the operational fabric.
A DefenseClaw-governed agent receiving Fabrix.ai’s operational context can identify that a combination of a memory leak trend on Service A, a deployment scheduled for Service B (which shares a database with Service A), and a capacity threshold approaching on the shared infrastructure is a pattern that preceded three P1 incidents in the last quarter , and can recommend preventive action before the incident materializes.
That’s MTTP. No amount of faster scanning or faster triage gets you there without the cross-domain operational intelligence that Fabrix.ai provides.
Governance Beyond Security Scanning
DefenseClaw covers security governance , skill scanning, code analysis, runtime content inspection, block/allow enforcement. These are critical capabilities for the “protect the world from agents” and “protect agents from the world” mandates Cisco articulated at RSAC.
But enterprise agentic operations require governance across a broader surface. Fabrix.ai’s Agentic Operational Model defines six pillars:
- Trust: Not just “is this agent safe?” (DefenseClaw) but “is this agent producing reliable, accurate operational insights?” Trust in agentic operations requires both security validation and outcome validation.
- Governance: Policy enforcement across the full operational lifecycle , not just agent admission and runtime security, but operational decision boundaries, escalation policies, and compliance frameworks.
- Security: Fabrix.ai recognizes and complements the security capabilities that DefenseClaw and NemoClaw provide. Security is essential but insufficient alone.
- Observability: Dual-plane visibility , security observability (DefenseClaw/Splunk) plus operational observability (Fabrix.ai) , giving enterprises complete awareness of both agent behavior and operational state.
- Explainability: Why did the agent correlate these events and recommend this action? DefenseClaw tells you what the agent did; Fabrix.ai’s context engine explains why, tracing the reasoning chain through the ontology.
- AgentOps: Full lifecycle management of operational agents , versioning, performance monitoring, drift detection, continuous tuning. The operational equivalent of DevOps applied to the agent fleet.
Better Together : NVIDIA + Cisco + Fabrix.ai
The architecture draws a clean line between three complementary roles:
| Stack Layer | Provider | Function |
| Agent Runtime Platform | NVIDIA NemoClaw + OpenShell | Sandboxed execution, local inference, privacy routing, policy enforcement |
| Agent Security Governance | Cisco DefenseClaw + Splunk Agentic SOC | Admission scanning, runtime enforcement, security telemetry, threat detection/response |
| Operational Data Intelligence | Fabrix.ai | Agentic Data Federation, ECL Ontology, cross-domain context, MTTP outcomes, AgentOps |
NemoClaw is the runtime. DefenseClaw is the governance. Fabrix.ai is the intelligence.
This is complementary positioning, not competitive. Fabrix.ai’s existing Cisco partnership and Splunk ITSI joint solutions work provide a natural go-to-market bridge. DefenseClaw streams telemetry to Splunk. Fabrix.ai enriches that telemetry with operational context. The Agentic SOC agents Cisco is rolling out through mid-2026 become dramatically more effective when they can reason over Fabrix.ai’s ontology rather than just raw security events.
The Bottom Line
The agentic AI industry is building increasingly sophisticated runtimes and increasingly sophisticated security. What it hasn’t built yet is the operational intelligence layer that makes agents actually useful for enterprise operations.
Agent runtime platforms solved the how , powerful tools, persistent memory, sub-agent spawning, self-evolution, OS-level access. Security stacks solved the trust , sandboxing, scanning, governance, enforcement.
What’s missing is the what, the enterprise operational context that agents need to reason about infrastructure, services, incidents, changes, dependencies, and business impact across fragmented data landscapes.
Fabrix.ai is that missing layer. Our Agentic Data Federation and ECL Ontology transform agent runtimes from powerful reasoning engines operating in a data vacuum into operational intelligence systems that can prevent incidents before they happen.
The runtime needs an intelligent engine. The agentic enterprise needs both.